
Digital forensics tools have improved a lot in the past several years. With these advances, the digital forensics community now has many tool options for each phase of an investigation.
In fact, there can be a lot of options to keep track of.
That’s why I wanted to bring together and curate the ultimate guide to DFIR tools — highlighting options available to examiners and when the best time to use them can be.
The advancements in digital forensic tools over the years have largely been driven by two things to meet evolving investigation needs: competition between more forensic software developers, and the maturation of the digital forensics open-source and research communities.
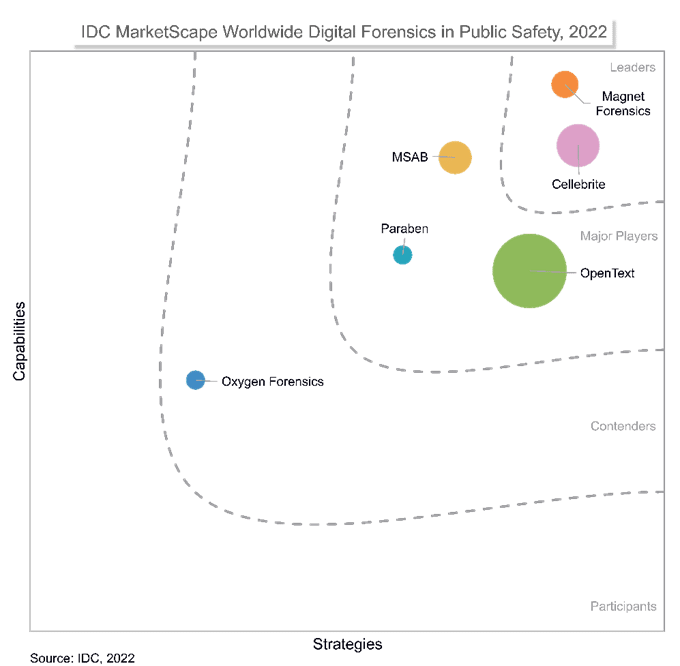
When it comes to the rise in competition between software providers, IDC has created a few in-depth reports comparing digital forensic tools for both private sector cyber security professionals and public sector digital investigators.
As for the maturation of the digital forensics research community, conferences like the Digital Forensics Research Workshop, the Open Source Digital Forensics Conference, and the Magnet Summit have been great opportunities for the community to get together and share knowledge and pain points. Whether closed or open-source, free or paid, I’m bringing you a comprehensive list of digital forensic tools to help you kit out a digital forensic library of any size.
This guide will focus on the tools you need to build a functioning general-purpose laboratory in either the public or private sector.
Digital Forensics Tools
Typically, a digital forensics library will have several digital forensics tools that do the same task. For example, several overlapping tools allow examiners to validate investigations results.
Whatever tooling you choose, ensure that you can get the same results using different methods. If you can’t, you must be able to explain why you can’t. Validation may mean manual parsing, conducting research, and reaching out to the forensics communities.
When choosing digital forensics tools for your toolkit, think about each part of your investigation workflow and the tasks that normally need to be completed. Comprehensive digital investigation toolkits support the most common investigation tasks. These toolkits can often include third-party or user-created artifacts or modules. Custom artifacts let a lab quickly develop parsers for newly observed sources of evidence, regardless of the underlying software tool. It’s worth learning how to write custom artifacts for your preferred toolkits.
Free, open-source forensics software tools are excellent for validating results. But outfitting an entire lab with free software can lead to a patchwork of tools that don’t always work together. Sometimes, this can make for complex and inefficient workflows and reduce your time to evidence. It’s recommended that a professional lab have at least one fully comprehensive software solution. Using tools that are well-recognized by courts will also save time, and smooth testimony at trial.
The following digital forensics tool lists are categorized using the first Digital Forensic Research Workshop investigative process for digital forensic science. Although proposed in 2001, the procedural concept is holding up surprisingly well. Let’s look at digital forensic tools and where they fit in identification, preservation, collection, examination, and analysis.
Identification
This is probably the most challenging part of any investigation. Before we can respond to an incident, we must detect it. Reporting could come from victims opening a case, a financial audit, or an admin checking their logs.
In criminal investigations, cases are typically reported to law enforcement. For private organizations, however, incident detection is critical. Passive measures like honeypots and canary tokens can greatly assist in alerting an organization to a compromise, while other tools can help with threat hunting Windows Event Logs and perform log analysis and incident response tasks.
Increasingly, users identify security incidents from threatening messages on the screen. Ransomware encrypts user files and demands payment for the decryption key.
Tools to assist in incident identification are either pre- or post-incident. Pre-incident monitoring often results in more data and higher fidelity. Post-incident analysis requires much more challenging event reconstruction, often with limited data. Corporate environments have control of their systems and may enable pre-incident monitoring with additional logging and detection systems. Law Enforcement, however, almost always deals with post-incident default (or disabled) logging and anti-forensics.
Preservation
Unfortunately, an incident has been identified and now you need to create a case, start documentation, and preserve any related data.
Case Management, Documentation and Reporting
Most comprehensive digital investigation toolkits require creating a “case” in the software before adding exhibits. Case management within your primary analysis tool may be possible; however, consider overall lab management and collaboration. An organization-wide case management system will provide better visibility and coordination.
Regardless of where case management tools are placed, ensure your investigators can easily document their processes and are supported in writing comprehensive reports. This support implies access to a knowledge base of commonly used legislation, definitions, references, and procedures.
Digital Forensic Imaging
Forensic imaging is both common and important in digital forensic investigations. But, imaging is not that easy. Resources like Practical Forensic Imaging are great for understanding the imaging process and challenges. Hardware and software can help making the imaging process easier, but validation still remains difficult.
Forensic Hardware Write Blocker and Disk Imagers
I talked before about what to look for in a write blocker. With any hardware write blocker, it is crucial to have a standard testing methodology that you local courts can accept and to test your hardware regularly.
Hardware write-blockers are highly reliable devices and typically only fail when misconfigured. Some write blockers allows you to disable write-block functions and use the device as a read/write hardware bridge. Be sure to include usage training and testing when adding hardware write blockers to your toolkit.
Most Linux-based forensic operating systems include software (kernel-level) write-blocking. There are several commercial write blockers for Windows, but they tend to be more expensive than hardware write-blockers. If you choose a software write-blocker, ensure you have a testing and validation procedure in place.
Disk Acquisition Software
Hardware and software write blockers need to be paired with imaging software. Hardware disk imagers have disk imaging software built-in; some external write blocker devices do not. Correct imaging is critical in any investigation, and the community is lucky to have such tools available for free.
In my personal opinion, and through experience, Magnet ACQUIRE does the job. For me, it is the best tool for physical and logical disk imaging as well as mobile device imaging. It allows investigators to quickly and easily acquire forensic images of any iOS or Android device, hard drive, and removable media. Best of all, it costs nothing.
With disk acquisition, be aware of how the acquisition software treats bad clusters. For example, some software may write 0’s where disk read fails. Others may skip and not write anything to the image. Imaging error response can lead to two different images from the same failing disk. Configure your imaging software to respond to errors according to your lab, or internal company SOP. Unfortunately, imaging software often does not allow error configurations and may not document their read failure procedure. In that case, you will need to test responses from different software and choose those that fit you and your DFIR teams’ needs best.
RAM Acquisition Software
Like disk imaging, labs should acquire RAM acquisitions from case-related systems. Random Access Memory (RAM) contains information about the system and user activities since the last time the computer was shut down. This might include information that will never be written to disk. As such, it can be a valuable source of evidence for investigators.
RAM is volatile, meaning that it changes quickly. If a computer or device is shut down, all data in RAM is cleared and cannot easily be recovered. First-responders need the tools and training to collect a RAM image from a live environment.
Many tools described in incident response can remotely collect a RAM image. Usually, tools are run for a prepared live data forensic toolkit on a USB stick or external storage medium. Remember that you will need an external storage location to save the memory dump.
Remember that RAM acquisition is complicated. You will need to load the tool into memory to acquire memory. As forensic examiners, we want to reduce the size of forensic tools in memory, so we don’t overwrite valuable evidence. Also, if the system is on, the RAM contents are changing every second. Imaging the same RAM twice will never result in the same image (and hash value, for that matter). Hash the RAM image after the acquisition, and the hash becomes your ground truth.
Mobile Acquisition Software Digital Forensics Tools
Just like computer forensics, mobile forensics is split into acquisition and analysis. Recently, more analysis toolkits include processing data from mobile devices. Acquisition, however, remains a huge challenge. Newer mobile devices are often secure, meaning that expensive software vulnerabilities are needed to acquire data from the device. Differences in geographic location also somewhat dictate device support.
Generally speaking, older devices often have publicly-released vulnerabilities and utilities to bypass disk protections. Commercial tools are more expensive, but the interface and resources are user-friendly. Commercial tools also (usually) include non-publicly released exploits for newer devices. Users can also request support and additional service for devices that are not yet supported.
Shot out to H-11 Digital Forensics and Rusolut for their chip-off kits and adapters. Most digital forensic laboratories do not have chip-off capabilities. As embedded devices become more popular, the need for chip-off will likely increase.
Invest in Your Investigators
The most valuable piece of your kit is you, and your team. Hardware, software, automation, and artificial intelligence can get you far. Still, a well-trained investigator must put the puzzle together to tell the story. Invest in your investigators.
SANS: an extensive range of high-quality training on information security and digital investigation topics.
NW3C: basic through advanced training related to various types of criminal investigations. Often free for Law Enforcement.
ECTEG: develops basic through advanced digital investigation training in the European Law.
DFIR Science and 13Cubed consistently produce digital investigation-related instruction videos on YouTube.
Similarly, the digital forensics community is relatively small but very active. There are some great resources like This Week in 4n6, DFIR Training, and About DFIR. Public and private sector experts often share information and resources and answer questions at the DFIR Discord as well as Forensic Focus.
Without further adieu, the must-have DFIR tools:

IR Tools Collection
Adversary Emulation
🔹APTSimulator: Windows Batch script that uses a set of tools and output files to make a system look as if it was compromised.
🔹Atomic Red Team (ART): Small and highly portable detection tests mapped to the MITRE ATT&CK Framework.
🔹AutoTTP: Automated Tactics Techniques & Procedures. Re-running complex sequences manually for regression tests, product evaluations, generate data for researchers.
🔹Blue Team Training Toolkit (BT3): Software for defensive security training, which will bring your network analysis training sessions, incident response drills and Red Team engagements to a whole new level.
🔹Caldera: Automated adversary emulation system that performs post-compromise adversarial behavior within Windows Enterprise networks. It generates plans during operation using a planning system and a pre-configured adversary model based on the Adversarial Tactics, Techniques & Common Knowledge (ATT&CK™) project.
🔹DumpsterFire: Modular, menu-driven, cross-platform tool for building repeatable, time-delayed, distributed security events. Easily create custom event chains for Blue Team drills and sensor/alert mapping. Red Teams can create decoy incidents, distractions, and lures support to scale their operations.
🔹Metta: Information security preparedness tool to do adversarial emulations.
🔹Network Flight Simulator: Lightweight utility used to generate malicious network traffic and help security teams to evaluate security controls and network visibility.
🔹Red Team Automation (RTA): RTA provides a framework of scripts designed to allow Blue Teams to test their detection capabilities against malicious tradecraft, modeled after MITRE ATT&CK™.
🔹RedHunt OS: Virtual machine for adversary emulation and threat hunting.
All-In-One-Tools
🔹Belkasoft Evidence Center: This toolkit will quickly extract digital evidence from multiple sources by analyzing hard drives, drive images, memory dumps, iOS, Blackberry and Android backups, UFED, JTAG, and chip-off dumps.
🔹CimSweep: Suite of CIM/WMI-based tools that enable the ability to perform incident response and hunting operations remotely across all versions of Windows.
🔹CIRTkit: CIRTkit is not just a collection of tools, but also a framework to aid in the ongoing unification of Incident Response and Forensics Investigation processes.
🔹Cyber Triage: Cyber Triage remotely collects and analyzes endpoint data to help determine if it is compromised. It’s agentless approach and focus on ease of use and automation allows companies to respond without major infrastructure changes and without a team of forensics experts. Its results are used to decide if the system should be erased or investigated further.
🔹Doorman: osquery fleet manager that allows remote management of osquery configurations retrieved by nodes. It takes advantage of osquery’s TLS configuration, logger, and distributed read/write endpoints, to give administrative visibility across a fleet of devices with minimal overhead and intrusiveness.
🔹Falcon Orchestrator: Extendable Windows-based application that provides workflow automation, case management and security response functionality.
🔹Flare: A fully customizable, Windows-based security distribution for malware analysis, incident response, and penetration testing.
🔹Fleetdm: State of the art host monitoring platform tailored for security experts. Leveraging Facebook’s battle-tested osquery project, Fleetdm delivers continuous updates, features and fast answers to big questions.
🔹GRR Rapid Response: Incident response framework on remote live forensics. It consists of a Python agent (client) that is installed on target systems, and a Python server infrastructure that can manage and talk to the agent. Besides the included Python API client, PowerGRR provides an API client library in PowerShell working on Windows, Linux and macOS for GRR automation and scripting.
🔹IRIS: IRIS is a web collaborative platform for incident response analysts allowing to share investigations at a technical level.
🔹Kuiper: Digital Forensics Investigation Platform
🔹Limacharlie: Endpoint security platform composed of a collection of small projects all working together that gives a user a cross-platform (Windows, OSX, Linux, Android and iOS) low-level environment for managing and pushing additional modules into memory to extend its functionality.
🔹Matano: Open-sources serverless security lake platform on AWS that lets you ingest, store, and analyze petabytes of data into an Apache Iceberg data lake and run near real-time Python detections as code.
🔹MozDef: Automates the security incident handling process and facilitates the near real-time activities of incident handlers.
🔹MutableSecurity: CLI program for automating the setup, configuration and use of cybersecurity solutions.
🔹nightHawk: Application built for asynchronous forensic data presentation using ElasticSearch as the backend. It’s designed to ingest Redline collections.
🔹Open Computer Forensics Architecture: Another popular distributed open-source computer forensics framework. This framework was built on the Linux platform and uses a postgreSQL database for storing data.
🔹osquery: Easily ask questions about your Linux and macOS infrastructure using a SQL-like query language; the provided incident-response pack helps you detect and respond to breaches.
🔹Redline: Provides host investigative capabilities to users to find signals of malicious activity through memory and file analysis, and the development of a threat assessment profile.
🔹The Sleuth Kit & Autopsy: Unix and Windows-based tool which helps in forensic analysis of computers. It comes with various tools which helps in digital forensics. These tools help in analyzing disk images, performing in-depth analysis of file systems, and various other things.
🔹TheHive: Scalable 3-in-1 open-source and free solution designed to make life easier for SOCs, CSIRTs, CERTs, and any information security practitioner dealing with security incidents that need to be investigated and acted upon swiftly.
🔹Velociraptor: Endpoint visibility and collection tool.
🔹X-Ways Forensics: Forensics tool for disk cloning and imaging. It can be used to find deleted files and performs disk analysis.
🔹Zentral: Combine’s osquery’s powerful endpoint inventory features with a flexible notification and action framework. This enables one to identify and react to changes on OSX and Linux clients.
Books
🔹Applied Incident Response: Steve Anson’s publication on Incident Response.
🔹Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory.
🔹Crafting the InfoSec Playbook: Security Monitoring and Incident Response Master Plan: by Jeff Bollinger, Brandon Enright and Matthew Valites.
🔹Digital Forensics and Incident Response: Incident Response Techniques and Procedures to Respond to Modern Cyber Threats: by Gerard Johansen.
🔹Introduction to DFIR: by Scott J. Roberts.
🔹Incident Response & Computer Forensics, Third Edition: The definitive guide to incident response.
🔹Incident Response Techniques for Ransomware Attacks: A great guide to build an incident response strategy for ransomware attacks, by Oleg Skulkin.
🔹Incident Response with Threat Intelligence: Great reference to build an incident response plan based also on Threat Intelligence, by Roberto Martinez.
🔹Intelligence-Driven Incident Response: By Scott J. Roberts, Rebekah Brown.
🔹Operator Handbook: Red Team + OSINT + Blue Team Reference: Great reference for incident responders, and one of my personal favorites. Best of both worlds combined.
🔹Practical Memory Forensics: The definitive guide to practice memory forensics. By Svetlana Ostrovskaya and Oleg Skulkin.
Communities
🔹Digital Forensics Discord Server: Community of 8,000+ working professionals from Law Enforcement, Private Sector, and Forensic Vendors. Additionally, plenty of students and hobbyists! Guide here.
🔹SANS DFIR Mailing List: Mailing list by SANS for DFIR.
🔹Slack DFIR Channel: Slack DFIR Community Channel — Signup here.
Disk Image Creation Tools
🔹AccessData FTK Manager: Forensics tool whose main purpose is to preview recoverable data from a disk of any kind. FTK Imager can also acquire live memory and paging file on 32bit and 64bit systems.
🔹Bitscout: Bitscout helps you build your fully-trusted customizable LiveCD/LiveUSB image to be used for remote digital forensics (or perhaps any other task of your choice). It is meant to be transparent and monitorable by the owner of the system, forensically sound, customizable and compact.
🔹GetData Forensic Imager: Windows-based program that will acquire, convert, or verify a forensic image in one of its many common forensic file formats.
🔹Guymager: Free forensic imager for media acquisition on Linux.
🔹Magnet ACQUIRE: ACQUIRE by Magnet Forensics allows various types of disk acquisitions to be performed on Windows, Linux, and OSX as well as mobile operating systems.
Evidence Collection
🔹artifactcollector: The artifactcollector project provides a software that collects forensic artifacts from systems.
🔹bulk_extractor: Computer forensics tool that scans a disk image, a file, or a directory of files and extracts useful information without parsing the file system or file system structures. Because of ignoring the file system structure, the program distinguishes itself in terms of speed and thoroughness.
🔹Cold Disk Quick Response: Streamlined list of parsers to quickly analyze a forensic image file (dd, E01, .vmdk, etc.) and output nine reports.
🔹CyLR: The CyLR tool collects forensic artifacts from hosts with NTFS file systems quickly, and securely and minimizes impact to the host.
🔹Forensic Artifacts: Digital Forensics Artifact Repository
🔹ir-rescue: Windows Batch script and a Unix Bash script to comprehensively collect host forensic data during incident response.
🔹Live Response Collection: Automated tool that collects volatile data from Windows, OSX, and *nix-based operating systems.
🔹Margarita Shotgun: Command-line utility (that works with or without Amazon EC2 instances) to parallelize remote memory acquisition.
🔹UAC: UAC (Unix-like-Artifacts Collector) is a Live Response collection script for Incident Response that makes use of native binaries and tools to automate the collection of AIX, Android, ESXi, FreeBSD, Linux, macOS, NetBSD, NetScaler, OpenBSD, and Solaris systems artifacts.
Incident Management
🔹Catalyst: A free SOAR system that helps to automate alert handling and incident response processes.
🔹CyberCPR: Community and commercial incident management tool with Need-to-Know built in to support GDPR compliance while handling sensitive incidents.
🔹Cyphon: Cyphon eliminates the headaches of incident management by streamlining a multitude of related tasks through a single platform. It receives, processes, and triages events to provide an all-encompassing solution for your analytic workflow — aggregating data, bundling and prioritizing alerts, and empowering analysts to investigate and document incidents.
🔹CORTEX XSOAR: Palo Alto Networks Security Orchestration and Response (SOAR) platform with full incident lifecycle management and many integrations to enhance automations.
🔹DFTimewolf: A framework for orchestrating forensic collection, processing and data export.
🔹DFIRTrack: Incident Response tracking application handling one or more incidents via cases and tasks with a lot of affected systems and artifacts.
🔹Fast Incident Response (FIR): Cybersecurity incident management platform designed with agility and speed in mind. It allows for easy creation, tracking, and reporting of cybersecurity incidents and is useful for CSIRTs, CERTs, and SOCs alike.
🔹RTIR: Request Tracker for Incident Response (RTIR) is the premier open-source incident handling system targeted for computer security teams who worked with over a dozen CERT and CSIRT teams from around the world to help you handle the ever-increasing volume of incident reports. RTIR builds on all the features of a Request Tracker.
🔹Sandia Cyber Omni Tracker (SCOT): Incident Response collaboration and knowledge capture tool focused on flexibility and ease-of-use. The goal is to add value to the incident response process without burdening the user.
🔹Shuffle: A general purpose security automation platform focused on accessibility.
🔹threat_note: Lightweight investigation notebook that allows security researchers the ability to register and retrieve indicators related to their research.
🔹Zenduty: Zenduty is a novel incident management platform providing end-to-end incident alerting, on-call management and response orchestration, giving teams greater control and automation over the incident management lifecycle.
Knowledge Bases
🔹Digital Forensics Artifact Knowledge Base: Digital Forensics Artifact Knowledge Base.
🔹Windows Events Attack Samples
🔹Windows Registry Knowledge Base
Linux Distributions
🔹The Appliance for Digital Investigation and Analysis (ADIA): VMware-based appliance used for digital investigation and acquisition and is built entirely from public domain software. Among the tools contained in ADIA are Autopsy, the Sleuth Kit, the Digital Forensics Framework, log2timeline, Xplico, and Wireshark. Most of the system maintenance uses Webmin. It is designed for small-to-medium sized digital investigations and acquisitions. The appliance runs under Linux, Windows, and macOS. Both i386 (32bit) and x86_64 (64bit) versions are available.
🔹Computer Aided Investigative Environment (CAINE): Contains numerous tools that help investigators during their analysis, including forensic evidence collection.
🔹CCF-VM: CyLR CDQR Forensics Virtual Machine (CCF-VM): An all-in-one solution to parsing collected data, making it easily searchable with built-in common searches, enabling search of single and multiple hosts simultaneously.
🔹Digital Evidence & Forensics Toolkit (DEFT): Linux distribution made for computer forensic evidence collection. It comes bundled with the Digital Advanced Response Toolkit (DART( for Windows. A light version of DEFT, called DEFT Zero is also available, which is focused primarily on forensically sound evidence collection.
🔹NST — Network Security Toolkit: Linux distribution that includes a vast collection of best-of-breed open-source network security applications useful to the network security professional.
🔹PALADIN: Modified Linux distribution to perform various forensics tasks in a forensically sound manner. It comes with many open-source forensics tools included.
🔹Security Onion: Special Linux distro aimed at network security monitoring featuring advanced analysis tools.
🔹SANS Investigative Forensic Toolkit (SIFT) Workstation: Demonstrates that advanced incident response capabilities are deep dive digital forensic techniques to intrusions can be accomplished using cutting-edge open-source tools that are freely available and frequently updated.
Linux Evidence Collection
🔹FastIR Collector Linux: FastIR for Linux collects different artifacts on live Linux and records the results in CSV files.
Log Analysis Tools
🔹AppCompatProcessor: AppCompatProcessor has been designed to extract additional value from enterprise-wide AppCompat/AmCache data beyond the classic stacking and grepping techniques.
🔹APT Hunter: APT Hunter is a Threat Hunting tool for Windows Event Logs.
🔹Chainsaw: Chainsaw provides a powerful ‘first-response’ capability to quickly identify threats within Windows Event Logs.
🔹Event Log Explorer: Tool developed to quickly analyze log files and other data.
🔹Event Log Observer: View, analyze, and monitor events recorded in Microsoft Windows Event Logs and with this GUI tool.
🔹Hayabusa: Hayabusa is a Windows Event Log fast forensics timeline generator and threat hunting tool.
🔹Kaspersky CyberTrace: Threat intelligence fusion and analysis tool that integrates threat data feeds with SIEM solutions. Users can immediately leverage threat intelligence for security monitoring and incident reporting (IR) activities in the workflow of their existing security operations.
🔹Log Parser Lizard: Execute SQL queries against structured log data: server logs, Windows Events, file system, Active Directory, log4net logs, comma/tab separated text, XML or JSON files. Also provides a GUI to Microsoft LogParser 2.2 with powerful UI elements: syntax editor, data grid, chart, pivot table, dashboard, query manager, and more.
🔹Lorg: Tool for advanced HTTPD logfile security analysis and forensics.
🔹Logdissect: CLI utility and Python API for analyzing log files and other data.
🔹LogonTracer: Tool to investigate malicious Windows logon by visualizing and analyzing Windows Event Logs.
🔹Sigma: Generic signature format for SIEM systems already containing an extensive ruleset.
🔹StreamAlert: Serverless, near real-time log data analysis framework, capable of ingesting custom data sources and triggering alerts using user-defined logic.
🔹SysmonSearch: SysmonSearch makes Windows Event Log analysis more effective and less time consuming by aggregation of event logs.
🔹WELA: Windows Event Log Analyzer: aims to be the Swiss Army knife for Windows Event Log management.
🔹Zircolite: A standalone and fast SIGMA-based detection tool for EVTX or JSON.
Memory Analysis Tools
🔹AVML: A portable volatile memory acquisition tool for Linux.
🔹Evolve: Web interface for the Volatility Memory Forensics Framework.
🔹inVtero.net: Advanced memory analysis for Windows x64 with nested hypervisor support.
🔹LiME: Loadable Kernel Module (LKM), which allows the acquisition of volatile memory from Linux and Linux-based devices, formerly called DMD.
🔹MalConfScan: MalConfScan is a Volatility plugin that extracts configuration data of known malware. Volatility is an open-source memory forensics framework for incident response and malware analysis. This tool searches for malware in memory images and dumps configuration data. In addition, this tool has a function to list strings to which malicious code refers.
🔹Memoryze: Free memory forensic software that helps incident responders find evil in live memory. Memoryze can acquire and/or analyze memory images and on live systems, can include the paging file in its analysis.
🔹Memoryze for Mac: Memoryze for Mac is Memoryze for Mac. A lower number of features, however.
🔹Orochi: Orochi is an open-source framework for collaborative forensic memory dump analysis.
🔹Rekall: Open-source tool (and library) for the extraction of digital artifacts from volatile memory (RAM) samples.
🔹Responder PRO: Responder PRO is the industry standard physical memory and automated malware analysis solution.
🔹Volatility: Advanced memory forensics network.
🔹Volatility 3: The volatile memory extraction framework (successor of Volatility).
🔹VolatilityBot: Automation tool for researchers cuts all the guesswork and manual tasks out of the binary extraction phase, or to help the investigator in the first steps of performing a memory analysis investigation.
🔹VolDiff: Malware Memory Footprint Analysis based on Volatility.
🔹WindowsSCOPE: Memory forensics and reverse engineering tool used for analyzing volatile memory offering the capability of analyzing the Windows kernel, DLLs, and virtual and physical memory.
Memory Imaging Tools
🔹Belkasoft Live RAM Capturer: Tiny free forensic tool to reliably extract the entire content of the computer’s volatile memory — even if protected by an active anti-debugging or anti-dumping system.
🔹Linux Memory Grabber: Script for dumping Linux memory and crating Volatility profiles.
🔹Magnet RAM Capture: Free imaging tool designed to capture the physical memory of a suspect’s computer. Supports recent versions of Windows.
🔹OSForensics: Tool to acquire live memory on 32bit and 64bit systems. A dump of an individual process’s memory space or physical memory dump can be done.
OSX Evidence Collection
🔹Knockknock: Displays persistent items (scripts, commands, binaries, etc.) that are set to execute automatically on OSX.
🔹macOS Artifact Parsing Tool (mac_apt): Plugin based on forensics framework for quick mac triage that works on live machines, disk images or individual artifact files.
🔹OSX Auditor: Free Mac OSX computer forensics tool.
🔹OSX Collector: OSX Auditor offshoot for live response.
🔹The ESF Playground: A tool to view the events in Apple Endpoint Security Framework (ESF) in near real-time.
Other Lists
🔹Awesome Event IDs: Collection of Event ID resources useful for Digital Forensics and Incident Response (DFIR).
🔹Awesome Forensics: A curated list of awesome forensic analysis tools and resources.
🔹Didier Stevens Suite: Tool collection.
🔹Eric Zimmerman Tools: An updated list of forensic tools created by Eric Zimmerman, an instructor who I’ve trained with at SANS.
🔹List of various Security APIs: Collective list of public JSON APIs for use in security.
Other Tools
🔹Cortex: Cortex allows you to analyze observables such as IP and email addresses, URLs, domain names, files or hashes one by one or in bulk mode using a Web interface. Analysts can also automate these operations using its REST API.
🔹Crits: Web-based tool which combines an analytic engine with a cyber threat database.
🔹Diffy: DFIR tool developed by Netflix’s SIRT that allows an investigator to quickly scope a compromise across cloud instances (Linux instances on AWS, currently) during an incident and efficiently triaging those instances for follow-up actions by showing differences against a baseline.
🔹domfind: Python DNS crawler for finding identical domain names under different TLDs.
🔹Fileintel: Pull intelligence per file hash.
🔹HELK: Threat Hunting platform.
🔹Hindsight: Internet history forensics for Google Chrome/Chromium.
🔹Hostintel: Pull intelligence per host.
🔹imagemounter: Command-line utility and Python package to ease the (un)mounting of forensic disk images.
🔹Kansa: Modular incident response framework in PowerShell.
🔹MFT Browser: MFT directory tree reconstruction and record information.
🔹Munin: Online hash checker for VirusTotal and other services.
🔹PowerSponse: PowerSponse is a PowerShell module focused on targeted containment and remediation during security incident response.
🔹PyaraScanner: Very simple multi-threaded many-rules to many-files YARA scanning Python script for malware zoos and IR.
🔹rastrea2r: Allows one to scan disks and memory for IOCs using YARA on Windows, Linux and OSX.
🔹RaQet: Unconventional remote acquisition and triaging tool that allows triaging for a disk of a remote computer (client) that is restarted with a purposely built forensic operating system.
🔹Raccine: A simple ransomware protection.
🔹Stalk: Collect forensic data about MySQL when problems occur
🔹Scout2: Security tool that lets Amazon Web Services administrators assess their environment’s security posture.
🔹Stenographer: Packet capture solution which aims to quickly spool all packets to disk, then provide simple, fast access to subsets of those packets. It stores as much history as possible, managing disk usage, and deleting when disk limits are hit. It’s ideal for capturing the traffic just before and during an incident, without the need to explicitly store all of the network traffic.
🔹sqhunter: Threat hunter based on osquery and Salt Open (SaltStack) that can issue ad-hoc or distributed queries without the need for osquery’s TLS plugin. sqhunter allows you to query open network sockets and check them against threat intelligence sources.
🔹sysmon-config: Sysmon configuration file template with default high-quality event tracing.
🔹sysmon-modular: A repository of sysmon configuration modules.
🔹traceroute-circl: Extended traceroute to support the activities of CSIRT (or CERT) operators. Usually, CSIRT teams have to handle incidents based on IP addresses received. Created by Computer Emergency Response Center, Luxembourg.
🔹X-Ray 2.0: Windows utility (poorly maintained or no longer maintained) to submit virus samples to AV vendors.
Playbooks
🔹AWS Incident Response Runbook Samples: AWS IR Runbook Samples meant to be customized per each entity using them. The three samples are: “DoS or DDoS attack,” “credential leakage,” and “unintended access to an Amazon S3 bucket.”
🔹Counteractive Playbooks: Counteractive Playbooks collection.
🔹GuardSIght Playbook Battle Cards: A collection of Cyber Incident Response Playbook Battle Cards.
🔹IRM: Incident Response Methodologies by CERT Societe Generale.
🔹IR Workflow Gallery: Different generic incident response workflows (e.g., for malware outbreak, data theft, unauthorized access, etc.). Every workflow consists of seven steps: prepare, detect, analyze, contain, eradicate, recover, post-incident handling. The workflows are online available for download.
🔹PagerDuty Incident Response Documentation: Documents that describe parts of the PagerDuty Incident Response process. It provides information not only on preparing for an incident, but also what to do during and after.
🔹Phantom Community Playbooks: Phantom Community Playbooks for Splunk yet also customizable for other use.
🔹ThreatHunter-Playbook: Playbook to aid the development of techniques and hypothesis for hunting campaigns.
Process Dump Tools
🔹Microsoft ProcDump: Dumps any running Win32 processes memory image on the fly.
🔹PMDump: Tool that lets you dump the memory contents of a process to a file without stopping the process.
Sandboxing/Reversing Tools
🔹AMAaaS: Android Malware Analysis as a Service, executed in a native Android environment.
🔹Any Run: Interactive online malware analysis service for dynamic and static research of most types of threats using any environment.
🔹CAPEv2: Malware Configuration and Payload Extraction.
🔹Cuckoo:: Open-source highly configurable sandboxing tool.
🔹Cuckoo-modified” Heavily modified Cuckoo fork developed by the community.
🔹Cuckoo-modified-api: Python library to control a cuckoo-modified sandbox.
🔹Cutter: Reverse engineering platform powered by Radare2.
🔹Ghidra: Software Reverse Engineering Framework.
🔹Hybrid-Analysis: Free powerful online sandbox by CrowdStrike.
🔹Intezer: Intezer Analyze dives into Windows binaries to detect micro-code similarities to known threats, to provide accurate yet easy-to-understand results.
🔹Joe Sandbox (Community): Joe Sandbox detects and analyzes potential malicious files and URLs on Windows, Android, macOS, Linux, and iOS for suspicious activities; providing comprehensive and detailed analysis reports.
🔹Mastiff: Static analysis framework that automates the process of extracting key characteristics from a number of different file formats.
🔹Metadefender Cloud: Free threat intelligence platform providing multi-scanning, data sanitization and vulnerability assessment of files.
🔹Radare2: Reverse engineering framework and command-line toolset.
🔹Reverse.IT: Alternative domain for the Hybrid-Analysis tool provided by CrowdStrike.
🔹Rizin: UNIX-like reverse engineering framework and command-line toolset.
🔹StringSifter: A machine learning tool that ranks strings based on their relevance for malware analysis.
🔹Threat.Zone: Cloud-based threat analysis platform which includes a sandbox, CDR and interactive analysis for researchers.
🔹Valkyrie Comodo: Valkyrie uses run-time behavior and hundreds of features from a file to performance analysis.
🔹Viper: Python-based binary analysis and management framework, that works well with Cuckoo and YARA.
🔹Virustotal: Free online service that analyzes files and URLs enabling the identification of viruses, worms, trojans and other kinds of malicious content detected by antivirus engines and website scanners.
🔹Visualize_Logs: Open-source visualization library and command-line tools for logs (Cuckoo, Procmon, more to come).
🔹Yomi: Free Multi-Sandbox managed and hosted by Yoroi.
Scanner Tools
🔹Fenrir: Simple IOC scanner. It allows scanning any Linux, Unix, OSX system for IOCs in plain Bash.
🔹LOKI: Free IR scanner for scanning endpoints with YARA rules and other Indicators of Compromise (IOCs).
🔹Spyre: Simple YARA-based IOC scanner written in Go.
Timeline Tools
🔹Aurora Incident Response: Platform developed to easily build a detailed timeline of an incident.
🔹Highlighter: Free tool available from Fire/Mandiant that will depict log/text file that can highlight areas on the graphic, that also corresponds to a keyword or phrase. Good for time-lining an infection and what was done post-compromise.
🔹Morgue: PHP Web app by Etsy for managing postmortems.
🔹Plaso: A Python-based backend engine for the tool log2timeline.
🔹Timesketch: Open-source tool for collaborative forensic timeline analysis.
Videos
🔹The Future of Incident Response: Presented by the brilliant Bruce Schneier at OWASP AppSecUSA 2015.
Windows Evidence Collection
🔹AChoir: Framework/scripting tool to standardize and simplify the process of scripting live acquisition utilities for Windows.
🔹Crowd Response: Lightweight Windows console application designed to aid in the gathering of system information for incident response and security engagements. It features numerous modules and output formats.
🔹DFIR ORC: DFIR ORC is a collection of specialized tools dedicated to reliably parsing and collecting critical artifacts such as the MFT, registry hives or event logs. DFIR ORC collects data, but does not analyze it: it is not meant to triage machines. It provides a forensically relevant snapshot of machines running Windows.
🔹FastIR Collector: Tool that collects different artifacts on live Windows systems and records the results in CSV files. With the analyses of these artifacts, an early compromise can be detected.
🔹Fibratus: Tool for exploration and tracing of the Windows kernel.
🔹Hoarder: Collects the most valuable artifacts for forensics or incident response investigations.
🔹IREC: All-in-one Evidence Collector which captures RAM Image, $MFT, Event logs, WMI Scripts, Registry Hives, System Restore Points and much more. It is free, lightning fast, and easy to use.
🔹Invoke-LiveResponse: Invoke-LiveResponse is a live response tool for targeted collection.
🔹IOC Finder: Free tool from Mandiant for collecting host system data and reporting the presence of Indicators of Compromise (IOCs). Support for Windows only. No longer maintained.
🔹IRTriage: Incident Response Triage — Windows evidence collection for forensic analysis.
🔹KAPE: Kroll Artifact Parser and Extractor (KAPE) — a triage tool that finds the most prevalent digital artifacts and then parses them quickly. Great and thorough when time is of the essence.
🔹LOKI: Free IR scanner for scanning endpoints with YARA rules and other Indicators of Compromise (IOCs).
🔹MEERKAT: PowerShell-based triage and threat hunting tool for Windows.
🔹Panorama: Fast incident overview on live Windows systems.
🔹PowerForensics: Live disk forensics platform using PowerShell.
🔹PSRecon: PSRecon gathers data from a remote Windows host using PowerShell (v2, or later), organizes the data into folders, hashes all the extracted data, hashes PowerShell and various system properties, and sends the data off to the security team. The data can be pushed to a share, sent over email, or retained locally.
🔹RegRipper: Open-source tool, written in Perl, for extracting/parsing information (keys, values, data) from the Registry and presenting it for analysis.
